Security Audits
We have the expertise to audit your current infrastructure. Give us a call at 252-492-4317.
Vulnerability Prevention
Vulnerability Prevention
Security Analysis
Security Analysis
About
Helpdesk Tickets
Login, create tickets and let us maintain your infrastructure.
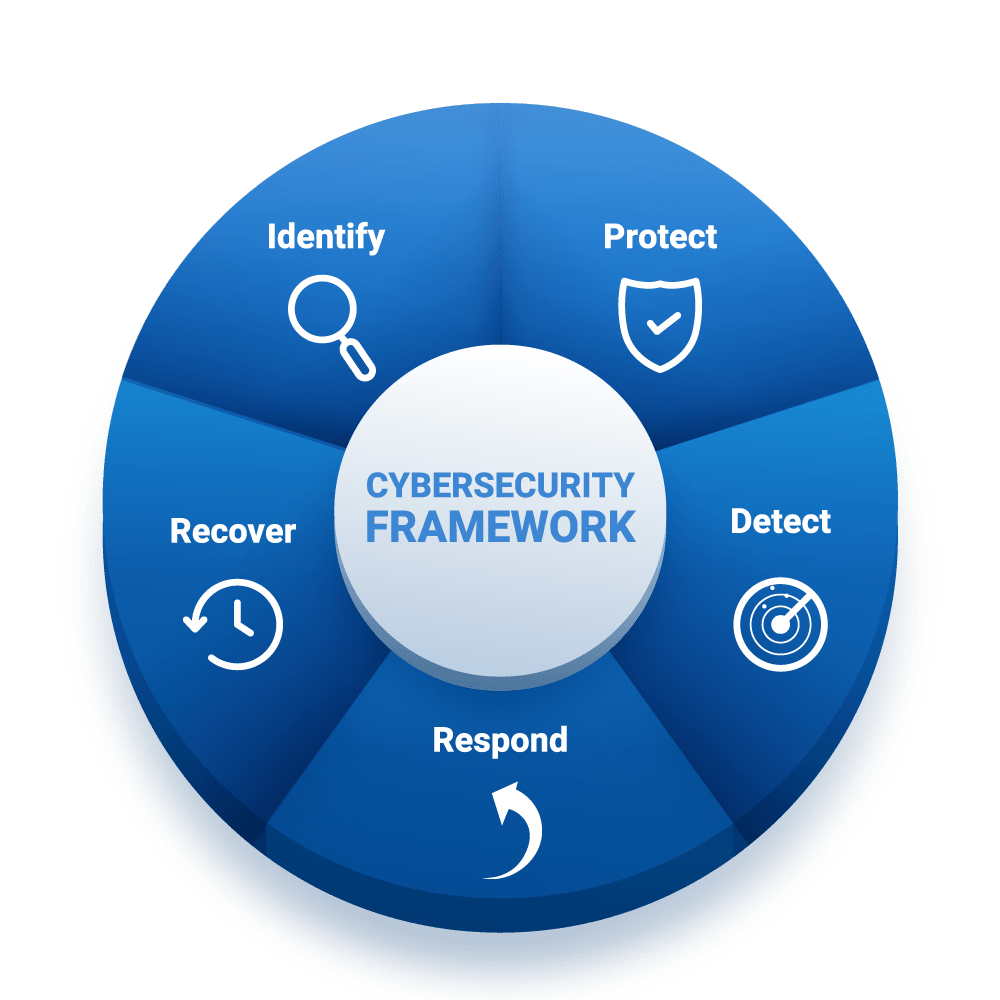
Cybersecurity Framework
The Framework is organized by five key Functions – Identify, Protect, Detect, Respond, Recover. These five widely understood terms, when considered together, provide a comprehensive view of the lifecycle for managing cybersecurity over time.
Features
What We Offer
Services to assist any size business survive the tangled, hazard layden vast of the Internet securely.
Professional IT Services
With our managed IT services in Houston, we help organizations find, design, implement, and manage the right technologies to improve the way they do business. We will do these and everything in between, so you can focus all your efforts on expanding your business.
Security Services
Donec sollicitudin molestie malesuada. Vivamus magna justo, lacinia eget consectetur sed
Hosted Services
We offer complete hosted Virtual Machines, email, websites or data backup. Offload your servers to our cloud over a secure Virtual Private Network.
Contact Us
(252) 492-4317
410 Dabney Drive, Henderson NC
Monday-Friday: 8am – 5pm
Get Started
Contact us to get started securing your data!


